Quick Answer: Cyber hygiene is the set of routine digital security habits – like strong unique passwords, software updates, and multi-factor authentication – that protect your devices, accounts, and personal data from cyber threats every day.
Most people lock their front door without thinking about it. Cyber hygiene is the same instinct applied online – small, consistent habits that stop threats before they become breaches.
The numbers make the case quickly. According to IBM’s 2024 Cost of a Data Breach Report, the average global breach cost hit $4.88 million in 2024 – a 10% jump, the largest year-over-year spike since the pandemic.
The FTC’s 2024 Consumer Sentinel Network Data Book reported over 1.1 million identity theft complaints in 2024 alone, with consumers losing more than $12.5 billion to fraud overall. And Microsoft research confirms that basic cybersecurity hygiene blocks 98% of attacks before they succeed.
The gap between “protected” and “compromised” is rarely a sophisticated zero-day exploit. It’s almost always a preventable gap – a reused password, an unpatched app, a clicked phishing link. Whether you’re a parent managing five family devices, a remote worker handling sensitive client data, or someone who just shops and banks online, cyber hygiene applies directly to you.
Table of Contents
- Key Takeaways
- What Is Cyber Hygiene? A Clear Cybersecurity Hygiene Definition
- Basic Cyber Hygiene Practices Everyone Should Follow
- Payment Hygiene: The Missing Layer in Cyber Hygiene
- Cyber Hygiene Best Practices: Your Daily Security Checklist
- Phishing Prevention and Malware Prevention Tips
- Data Protection Best Practices: Identity, Privacy, and Device Security
- Cyber Hygiene for Businesses, Remote Workers, and Small Business Security
- Cyber Hygiene, Compliance, and Regulatory Frameworks
- Making Cyber Hygiene a Daily Habit: Tools That Do the Work for You
- The Bottom Line on Cyber Hygiene
- Frequently Asked Questions
- Sources
Key Takeaways
- Cyber hygiene is the set of routine security practices – strong passwords, software updates, MFA, and data backups – that protect your devices and personal data from cyber threats.
- Basic cybersecurity hygiene protects against 98% of attacks, according to Microsoft.
- Multi-factor authentication alone prevents 99.9% of automated account compromise attacks, per Microsoft – making it the single highest-impact habit most people skip.
- The FTC received over 1.1 million identity theft reports in 2024, and total fraud losses hit $12.5 billion – poor cyber hygiene is a direct contributor.
- Stolen credentials are the top initial attack vector in breaches, appearing in 88% of system-intrusion incidents, per the 2025 Verizon DBIR – a problem a password manager solves directly.
- Explore Batten’s password managers and identity protection services to automate the most critical cyber hygiene habits.
What Is Cyber Hygiene? A Clear Cybersecurity Hygiene Definition
Cyber hygiene – also called cybersecurity hygiene – refers to the practices and habits that keep your digital environment healthy and protected from threats. CISA (Cybersecurity and Infrastructure Security Agency) describes it as the baseline behavior every person and organization should maintain: strong passwords, software updates, multi-factor authentication, and careful behavior around links and attachments.
Think of it the way you think about dental hygiene. Skip brushing once and nothing dramatic happens. Skip it for a year and you face serious, expensive consequences. The same logic applies online. Poor cyber hygiene doesn’t cause a breach on day one – it creates vulnerabilities that attackers eventually find and exploit.
The cyber hygiene definition has two layers:
- Personal Cyber Hygiene: The habits individuals practice to secure their own accounts, devices, and identity – from password management to safe browsing.
- Organizational Cyber Hygiene: The policies, processes, and tools businesses use to protect employee access, customer data, and network infrastructure.
Both start from the same foundation: consistency. A single update or strong password doesn’t make you secure. Doing these things repeatedly, automatically, and across all your devices does.

Basic Cyber Hygiene Practices Everyone Should Follow
These are the non-negotiables – the daily habits that form the backbone of personal cybersecurity. None require technical expertise. All take less time than you’d expect.
Password Hygiene Best Practices
Weak and reused passwords remain one of the most reliable entry points for attackers. The 2025 Verizon Data Breach Investigations Report found that stolen or compromised credentials are the top initial attack vector, appearing in 88% of system-intrusion breaches. Credential abuse (22%) and exploited vulnerabilities (20%) together account for nearly half of all confirmed breach entry points.
The fix is direct: use a password manager to generate and store unique, complex passwords for every account. Tools like Keeper, NordPass, Dashlane, and 1Password handle this entirely – you remember one master password and they handle the rest. No spreadsheets, no sticky notes, no reused passwords.

- Password Length: Use at least 16 characters mixing letters, numbers, and symbols.
- Unique Passwords: Never reuse passwords across accounts – one compromised account cascades into many.
- Password Manager: Store all credentials in an encrypted vault with zero-knowledge architecture.
- Regular Audits: Review saved passwords quarterly and immediately update any flagged as weak, reused, or exposed in a known breach.
Contact Batten Black to get a personalized cyber hygiene audit.
Multi-Factor Authentication: The Single Highest-Impact Action
Enable MFA on every account that supports it – email, banking, social media, and cloud storage especially. Microsoft’s research shows MFA blocks 99.9% of automated credential attacks. It takes under 60 seconds to set up and eliminates the most common attack vector entirely.
Even if an attacker has your password – whether from a phishing attempt, a corporate breach, or credential-stuffing – they can’t log into your account without passing the second factor. That second factor is typically a code from an authenticator app that expires every 30 seconds.
Software Update Security Practices and Patch Management
Cybercriminals actively scan for unpatched devices. The 2025 Verizon DBIR found that exploitation of vulnerabilities surged 34% year-over-year, making unpatched software one of the fastest-growing attack vectors. Running outdated operating systems and apps is the digital equivalent of leaving a window unlocked.
Enable automatic updates on all devices – phones, laptops, tablets, routers, and smart home gadgets. Don’t delay prompts to restart after updates. Those updates frequently patch vulnerabilities that are already being actively exploited in the wild.
Payment Hygiene: The Missing Layer in Cyber Hygiene
Most cyber hygiene advice focuses on passwords, MFA, and software updates. That covers account access, but it leaves one major gap: your payment data.
Every time you reuse the same card across multiple sites, you increase your exposure. A single retailer breach, compromised checkout page, or phishing attempt can put your entire financial account at risk.
Payment hygiene closes that gap. Using virtual cards replaces your real card details with unique, transaction-specific numbers. If one card is exposed, it can be locked or deleted instantly without affecting anything else.
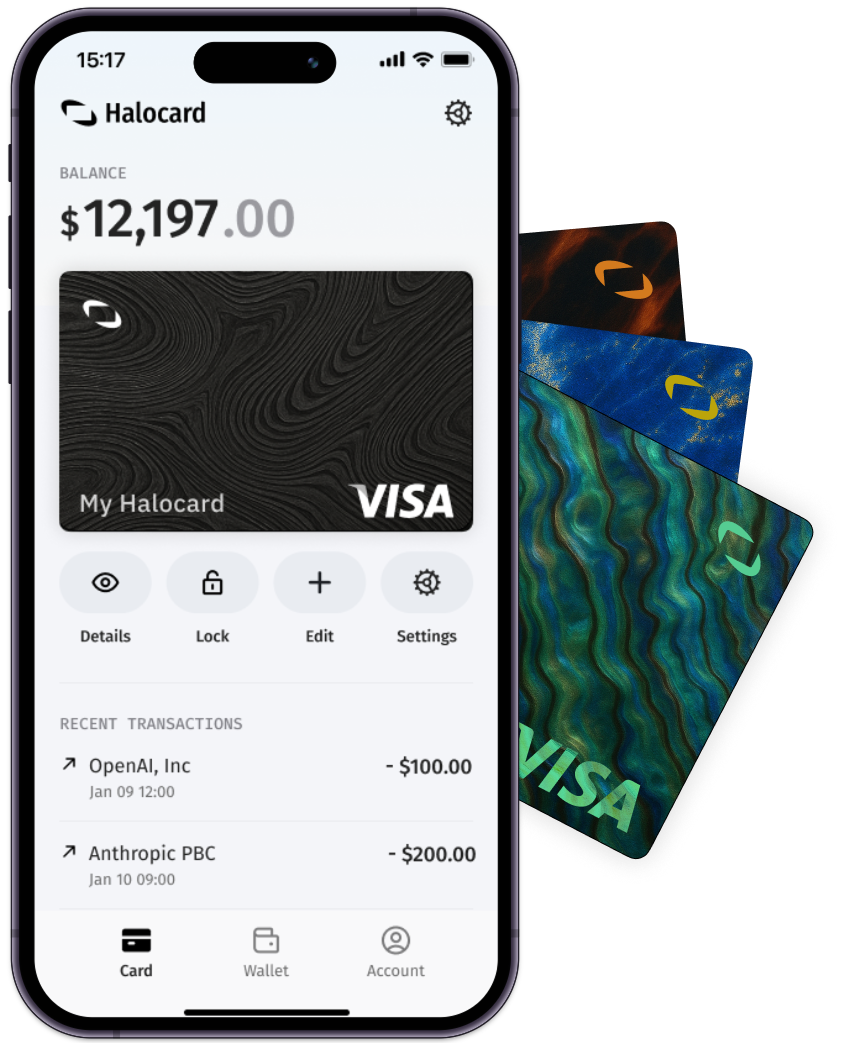
Tools like Halocard make this easy to implement. You can create a new card for each purchase or subscription, set spending limits, and monitor activity in real time. It is a simple layer that dramatically reduces the impact of payment-related breaches.
Cyber Hygiene Best Practices: Your Daily Security Checklist
| Practice | Why It Matters | How Often |
| Update software and OS | Patches known vulnerabilities attackers exploit | Enable automatic updates |
| Use unique passwords via manager | Prevents credential-stuffing and reuse attacks | When creating new accounts |
| Enable MFA on all accounts | Blocks 99.9% of automated login attacks | Set up once, works continuously |
| Back up important data | Protects against ransomware and device loss | Daily or weekly (automated) |
| Review account activity | Catches unauthorized access early | Monthly |
| Run phishing awareness training | Reduces chance of clicking malicious links | Ongoing |
| Monitor dark web for exposed credentials | Alerts you if login details are sold online | Continuous via ID protection service |
| Audit app permissions | Revokes unnecessary access to camera, mic, location | Quarterly |
| Use virtual cards for online purchases | Prevents card data exposure | Every online purchase |
Phishing Prevention and Malware Prevention Tips
Phishing drives between 80–95% of all human-related breaches, according to Comcast Business security research. Attackers disguise malicious emails as trusted senders – banks, delivery services, employers, even friends whose accounts may be compromised – to steal credentials or install malware with a single click.

These are the defensive habits that actually work:
- Verify the Sender Address: Check the actual email domain, not just the display name. “Amazon Support” can mask a completely unrelated domain.
- Hover Before Clicking: Preview every link destination URL before opening it. Mismatched domains are a red flag.
- Never Open Unexpected Attachments: Even from known contacts – their account may have been compromised and used to deliver malware.
- Use a VPN on Public Wi-Fi: Public networks are prime interception points for credential theft. A VPN like NordVPN or ExpressVPN encrypts all traffic, so anyone on the same public network sees nothing useful. See Batten’s breakdown of whether a VPN is worth it for a full explanation of when and why VPNs matter.
- Check Before You Trust: If an email creates urgency around account access, financial transfers, or password resets, verify directly through the official website or phone number – not a link in the email.

Data Protection Best Practices: Identity, Privacy, and Device Security
Identity theft is frequently a direct consequence of poor cyber hygiene. When credentials are reused, unmonitored, or exposed in a data breach, criminals can open fraudulent accounts, drain funds, and destroy credit – often for months or years before victims notice. The FTC reported that identity theft was the second most reported category in 2024, accounting for 18% of all Sentinel reports.
Identity protection services like NordProtect, Identity Guard, Cloaked, and IDShield provide continuous dark web monitoring, credit change alerts, SSN monitoring, and in many cases dedicated recovery specialists who help you reclaim your identity if it’s compromised. Think of them as a real-time early warning system and a safety net combined.
The importance of these services goes beyond detection. Stolen credentials are often listed on dark web marketplaces for months before being actively used – identity monitoring services can alert you in that window, before the damage compounds. See Batten’s overview of identity theft protection benefits to understand what these services actually cover and when they’re worth it.

Device and Network Security Hygiene
Strong device and network hygiene closes the physical and local attack surface that software-only measures miss.
- Lock Your Devices: Use screen lock with PIN, fingerprint, or face recognition on every device, including tablets and laptops. A lost unlocked device is an open account.
- Secure Your Home Wi-Fi: Change your router’s default admin password, use WPA3 encryption where available, and place IoT devices on a separate guest network segment. See Batten’s home wireless router security guide for step-by-step configuration.
- Encrypt Sensitive Data: Enable full-disk encryption (FileVault on Mac, BitLocker on Windows) on all laptops holding financial or personal data. Encryption renders a stolen device’s contents unreadable without the decryption key.
- Audit App Permissions Regularly: Review which apps access your camera, microphone, location, and contacts. Revoke permissions that aren’t actively needed. Mobile apps frequently request more access than they require to function.
- Secure Baby Monitors and Smart Home Devices: IoT devices are a growing attack surface. Change default passwords, keep firmware updated, and isolate them on a separate network. Batten’s hack-proof baby monitor guide covers the specific risks and solutions for connected home devices.

Cyber Hygiene for Businesses, Remote Workers, and Small Business Security
Remote workers face a unique challenge: no IT department watching their back. According to IBM, a data breach costs an average of $173,074 more when remote work is a contributing factor. The Canadian Centre for Cyber Security’s 2025 guidance notes that even sophisticated attackers typically exploit common, predictable vulnerabilities for initial access – precisely the gaps that good cyber hygiene closes.
For home office protectors and small business owners, these are the priority controls:
| Practice | Applies To | Priority Level |
| Mandatory MFA for all business logins | All employees and accounts | Critical |
| Regular security awareness training | All staff | High |
| Scheduled patch management | IT administrators | Critical |
| Least-privilege access controls | IT and account admins | High |
| VPN required on all non-office networks | Remote workers | High |
| Vendor and third-party access reviews | Management | Medium |
| Written incident response plan | Business leadership | High |
| Separate devices for work and personal use | Remote workers | Medium |
For remote workers and home office setups, pairing a VPN with a password manager and MFA replicates most of what a corporate IT department provides. That combination encrypts traffic, eliminates credential reuse, and closes the two most common initial access vectors.
The dark web also poses specific risks for businesses. Compromised employee credentials are frequently sold and used for corporate account takeovers. Batten’s guide to dark web dangers explains how stolen data moves through criminal networks and what organizations can do to monitor for exposure.
Cyber Hygiene, Compliance, and Regulatory Frameworks
Strong cyber hygiene isn’t just sound practice – it’s frequently required by law. Regulatory frameworks including NIST, GDPR, HIPAA, SOC 2, and PCI-DSS all mandate baseline security controls that map directly to cyber hygiene practices.
For small businesses especially, cyber hygiene isn’t about achieving security perfection. It’s about eliminating the easy wins for attackers – patching software, enforcing strong credentials, training your team, monitoring for threats. These actions require modest investment and prevent a disproportionate amount of damage.
Making Cyber Hygiene a Daily Habit: Tools That Do the Work for You
The hardest part of cyber hygiene isn’t knowing what to do – it’s doing it consistently across every device, account, and user in your household or organization. The practical answer is automation.
- Automate Software Updates: Set all devices to update automatically. Patches apply without you thinking about it.
- Use a Password Manager: Every account gets a strong, unique, randomly generated password. You remember one master credential; the manager handles the rest.
- Set Up Identity Monitoring: A good identity protection service alerts you immediately when your personal data or credentials surface on the dark web, in breaches, or in fraudulent credit applications.
- Enable MFA App-Wide: Use an authenticator app (not SMS where possible) and activate MFA on email, banking, social media, and any accounts holding financial or personal information.
- Use a VPN When Away from Home: Public Wi-Fi at coffee shops, airports, and hotels is frequently unencrypted and easily monitored. A VPN closes that gap automatically at connection.
Once these tools are configured, your ongoing time investment drops to minutes a week. The cost of skipping them – financially, legally, and practically – is orders of magnitude higher.
For a broader look at building layered digital protection for your household or business, see Batten’s family cybersecurity plan.
The Bottom Line on Cyber Hygiene
Cyber hygiene is not about complexity. It is about consistency. Most cyberattacks succeed because of simple, preventable gaps like weak passwords or missed updates.
Set up the basics once, automate what you can, and let those habits run in the background. That is how you stay protected without overthinking it.
Ready to make cyber hygiene automatic? Start with Batten’s password managers and identity protection services – the two tools that handle the most critical daily security habits so you don’t have to think about them.
Frequently Asked Questions
What Is the Cyber Hygiene Definition in Simple Terms?
Cyber hygiene is the set of routine digital security habits – like using strong unique passwords, keeping software updated, enabling multi-factor authentication, and backing up data – that protect your accounts and devices from cyber threats. Like physical hygiene prevents illness, cyber hygiene prevents breaches by addressing vulnerabilities before attackers find them.
What Are Examples of Basic Cyber Hygiene Practices?
Practical examples include using a password manager for all accounts, enabling MFA on email and banking apps, turning on automatic OS updates, locking devices with biometrics, running a VPN on public Wi-Fi, monitoring your credit through an identity protection service, and backing up files to encrypted cloud storage or an external drive.
How Often Should Cyber Hygiene Be Done?
MFA and automatic software updates work in the background continuously. Other practices need periodic attention: review account activity monthly, audit app permissions quarterly, update passwords on compromised accounts immediately, and back up important data weekly. An annual full security review – covering all accounts, devices, and connected services – helps catch gaps that accumulate over time.
Why Is Cyber Hygiene Important for Families and Remote Workers?
The FTC received over 1.1 million identity theft reports in 2024. For families, poor hygiene puts children’s information and financial accounts at risk. For remote workers, it means no IT safety net – breaches cost an average $173,000 more when remote work is a factor, per IBM. Both groups benefit most from automated tools that enforce strong habits across all household or work devices.
What Happens Without Good Cyber Hygiene?
Poor cyber hygiene creates predictable gaps. Outdated software exposes known vulnerabilities. Reused passwords mean one breach unlocks multiple accounts. Without monitoring, stolen credentials are often sold on the dark web and used for months before victims notice. The 2025 Verizon DBIR found ransomware in 44% of all confirmed breaches, with small businesses bearing the heaviest impact at 88% ransomware prevalence.
How Does Cyber Hygiene Relate to Identity Theft Prevention?
Identity theft is a direct downstream consequence of poor cyber hygiene. Reused passwords, unmonitored credentials, and lack of MFA all create easy pathways for criminals to impersonate victims.
What Is the Difference Between Cyber Hygiene and a Cybersecurity Strategy?
Cyber hygiene is the routine preventive foundation – the habits every individual and organization should maintain daily. A full cybersecurity strategy adds layers on top: advanced threat detection, incident response planning, security architecture, compliance frameworks, and continuous monitoring. You can maintain good cyber hygiene without being a security professional, but no cybersecurity strategy is effective without a solid hygiene foundation underneath it.
Sources
- “IBM Report: Escalating Data Breach Disruption Pushes Costs to New Highs,” July 2024, IBM Newsroom, https://newsroom.ibm.com/2024-07-30-ibm-report-escalating-data-breach-disruption-pushes-costs-to-new-highs
- “Consumer Sentinel Network Data Book 2024,” March 2025, Federal Trade Commission, https://www.ftc.gov/reports/consumer-sentinel-network-data-book-2024
- “New FTC Data Show a Big Jump in Reported Losses to Fraud to $12.5 Billion in 2024,” March 2025, Federal Trade Commission, https://www.ftc.gov/news-events/news/press-releases/2025/03/new-ftc-data-show-big-jump-reported-losses-fraud-125-billion-2024
- “One Simple Action You Can Take to Prevent 99.9 Percent of Account Attacks,” August 2019, Microsoft Security Blog, https://www.microsoft.com/en-us/security/blog/2019/08/20/one-simple-action-you-can-take-to-prevent-99-9-percent-of-account-attacks/
- “2025 Data Breach Investigations Report,” April 2025, Verizon Business, https://www.verizon.com/business/resources/reports/dbir/
- “Verizon’s 2025 DBIR: Alarming Surge in Cyberattacks Through Third-Parties,” April 2025, Verizon About, https://www.verizon.com/about/news/2025-data-breach-investigations-report
- “Cybersecurity Best Practices,” 2025, Cybersecurity and Infrastructure Security Agency (CISA), https://www.cisa.gov/topics/cybersecurity-best-practices
- “Cyber Security Hygiene Best Practices for Your Organization – ITSAP.10.102,” September 2025, Canadian Centre for Cyber Security, https://www.cyber.gc.ca/en/guidance/cyber-security-hygiene-best-practices-your-organization-itsap10102
- “What Is Cyber Hygiene? Overview & Best Practices,” 2026, Tenable, https://www.tenable.com/cybersecurity-guide/learn/what-is-cyber-hygiene
- “Cyber Security Breaches Survey 2025,” 2025, UK Department for Science, Innovation and Technology, https://www.gov.uk/government/statistics/cyber-security-breaches-survey-2025/cyber-security-breaches-survey-2025




